

Salesforce is warning customers that hackers are targeting websites with misconfigured Experience Cloud platforms that give guest users access to more data than intended. However, the ShinyHunters extortion gang claims to be actively exploiting a new bug to steal data from instances.
Salesforce has shared guidance for its customers to defend against hackers actively targeting the /s/sfsites/aura API endpoint on misconfigured Experience Cloud instances that gives guest users access to more data than intended.
The company states that attackers are deploying a modified version of AuraInspector, an open-source auditing tool developed by Mandiant, which can help administrators identify access control misconfigurations within the Salesforce Aura framework.
“It is important to note that Salesforce remains secure, and this issue is not due to any vulnerability inherent to our platform. Our investigation to date confirms that this activity relates to a customer-configured guest user setting, not a platform security flaw,” Salesforce says in the advisory.
The company explains that a publicly exposed Salesforce Experience site accepts a “guest user profile” to provide anonymous, unauthenticated visitors with access to data intended to be public. If the profile is misconfigured and has excessive permissions, visitors can “directly query Salesforce CRM objects without logging in.”
Salesforce says an organization can improve its defenses against such attacks by auditing guest user permissions and adopting the principle of least privilege.
The vendor says the highest-impact change customers can make to mitigate the risk is to disable guest access to public APIs and remove the API Enabled setting from the guest profile.
The company recommends customers take the following set of immediate actions:
- Audit guest user permissions and reduce them to the minimum required.
- Set org-wide defaults to Private for external access.
- Turn off Portal User Visibility and Site User Visibility so guest users cannot enumerate internal users.
- Disable self-registration unless it is truly needed, because exposed guest data could be used to create portal accounts and expand access.
System administrators should also review Aura Event Monitoring logs for unusual access patterns, unfamiliar IP addresses, or queries against objects that should not be public, and designate a Security Contact so Salesforce can notify the right person quickly.
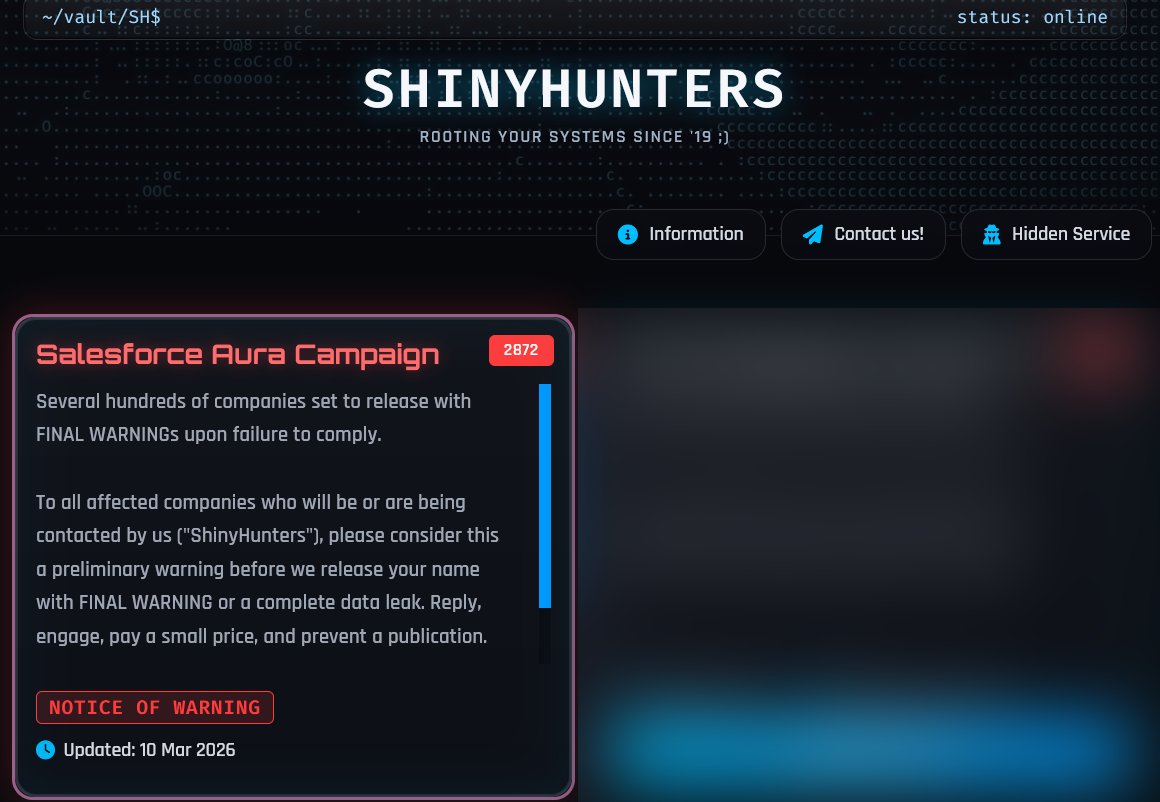
ShinyHunters takes responsibility
In a post on their data leak site, the ShinyHunters threat actor has claimed responsibility for the Salesforce Aura/Experience Cloud data theft attacks.
Mandiant Consulting confirmed in a statement for BleepingComputer that hackers are using AuraInspector in attempts to breach companies.
“We are aware of a threat actor attempting to facilitate intrusions by misusing the AuraInspector open-source tool to automate vulnerability scans across Salesforce environments,” said Charles Carmakal, Mandiant chief technology officer.
“We are working closely with Salesforce and our customers to provide the necessary telemetry and detection rules to mitigate potential risk. It is important to note that detecting scanning activity in an organization’s logs does not indicate a compromise,” the CTO said.
ShinyHunters says that they compromised around 100 high-profile companies, many of them in the cybersecurity sector. The total count of breached organizations is somewhere between 300 and 400, the hackers told BleepingComputer.
source: BleepingComputer
The hackers told BleepingComputer that in September 2025, they started to compromise companies with insecure Experience Cloud access control configurations for guest users. They were also identifying Aura instances by scanning the internet for the /s/sfsites/ endpoint.
Due to a limitation from Salesforce, the threat actor said that they could only query 2,000 records at a time through the company’s GraphQL API, which slowed the data theft process. However, the hacker found the sortBy parameter, which they claim bypassed the restriction.
When AuraInspector was released in January to help admins find misconfigured instances, ShinyHunters says they modified the code for additional reconnaissance. Salesforce’s advisory confirms that the threat actor’s variant of Mandiant’s tool was used “to perform mass scanning of public-facing Experience Cloud sites.”
The threat actors then created their own tool to steal data, which BleepingComputer has learned uses the following string as part of its user agent:
Anthropic/RapeForceV2.01.39 (AGENTIC)
This tool has a similar name to the “RapeFlake” tool used during the SnowFlake data theft attacks.
ShinyHunters claims that after Salesforce fixed the sortBy trick previously noted by Mandiant, they discovered a new method to bypass the 2,000 record query restriction, “and have been exploiting it since discreetly.”
The threat actor claims that Salesforce fixed the method used to bypass the 2,000-record limit over the weekend before releasing the advisory, but says they have since discovered a vulnerability that allows data theft from Aura instances even when they are properly configured.
BleepingComputer has not been able to independently confirm if this is true. We contacted Salesforce about this allegedly new attack, but the company continues to state that there is no vulnerability in its platform.
The threat actor told BleepingComputer that they believe disabling “Public Access” to an instance will protect Salesforce customers against this new attack. However, doing so will also disable guest access and turn the website into a private portal.
The threat actor told BleepingComputer that the new attacks are using the following user agent, which looks like a normal browser user agent.
Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 Chrome/120.0.0.0 Safari/537.36
Surprisingly, the threat actor told BleepingComputer that they believe that Salesforce customers can protect themselves from these attacks by disabling “Public Access” to an instance.
However, doing so will also disable guest access and turn the website into a private portal.
