A dual Russian and Israeli national has been charged in the United States for allegedly being the developer of the now-defunct LockBit ransomware-as-a-service (RaaS) operation since its inception in or around 2019 through at least February 2024.
Rostislav Panev, 51, was arrested in Israel earlier this August and is currently awaiting extradition, the U.S. Department of Justice (DoJ) said in a statement. Based on fund transfers to a cryptocurrency wallet owned by Panev, he allegedly earned approximately $230,000 between June 2022 and February 2024.
“Rostislav Panev for years built and maintained the digital weapons that enabled his LockBit co-conspirators to wreak havoc and cause billions of dollars in damage around the world,” U.S. Attorney Philip R. Sellinger said.
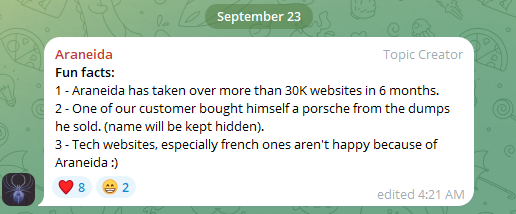
LockBit, which was one of the most prolific ransomware groups, had its infrastructure seized in February 2024 as part of an international law enforcement operation called Cronos. It gained notoriety for targeting more than 2,500 entities in at least 120 countries around the world, including 1,800 in the U.S. alone.
Victims of LockBit’s attacks included individuals and small businesses to multinational corporations, such as hospitals, schools, nonprofit organizations, critical infrastructure, government, and law enforcement agencies. The RaaS is believed to have netted the group at least $500 million in illicit profits.
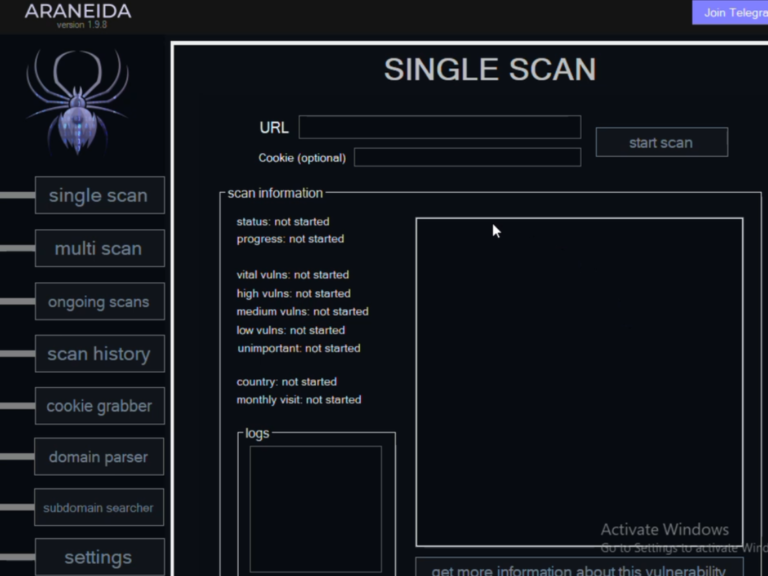
Court documents show that Panev’s computer analyzed following his arrest had administrator credentials for an online repository that was hosted on the dark web and contained source code for multiple versions of the LockBit builder, which affiliates used to create custom builds of the ransomware.
Also discovered were access credentials for the LockBit control panel and a tool called StealBit, which allowed the affiliate actors to exfiltrate sensitive data from compromised hosts prior to initiating the encryption process.
Panev, besides writing and maintaining the LockBit malware code as well as offering technical guidance to the e-crime group, is also accused of exchanging direct messages with Dmitry Yuryevich Khoroshev, the primary administrator who also went by online alias LockBitSupp, discussing development work related to the builder and control panel.
“In interviews with Israeli authorities following his arrest in August, Panev admitted to having performed coding, development, and consulting work for the LockBit group and to having received regular payments in cryptocurrency for that work,” the DoJ said.
“Among the work that Panev admitted to having completed for the LockBit group was the development of code to disable antivirus software; to deploy malware to multiple computers connected to a victim network; and to print the LockBit ransom note to all printers connected to a victim network.”
With the latest arrest, a total of seven LockBit members – Mikhail Vasiliev, Ruslan Astamirov, Artur Sungatov, Ivan Gennadievich Kondratiev, Mikhail Pavlovich Matveev – have been charged in the U.S.
Despite these operational setbacks, the LockBit operators appear to be plotting a comeback, with a new version LockBit 4.0 scheduled for release in February 2025. However, it remains to be seen if the extortion gang can successfully stage a return in light of the ongoing wave of takedowns and charges.
Second Netwalker Ransomware Affiliate Gets 20 Years in Prison
The development comes as Daniel Christian Hulea, a 30-year-old Romanian affiliate of the NetWalker ransomware operation, was sentenced to 20 years in prison and ordered to forfeit $21,500,000 and his interests in an Indonesian company and a luxury resort property that was financed with ill-gotten proceeds from the attacks.
Hulea previously pleaded guilty in the U.S. to charges of computer fraud conspiracy and wire fraud conspiracy back in June 2024. He was arrested in Romania on July 11, 2023, and subsequently extradited to the U.S.
“As part of his plea agreement, Hulea admitted to using NetWalker to obtain approximately 1,595 bitcoin in ransom payments for himself and a co-conspirator, valued at approximately $21,500,000 at the time of the payments,” the DoJ said.
The NetWalker ransomware operation particularly singled out the healthcare sector during the height of the COVID-19 pandemic. It was dismantled online in January 2021 when U.S. and Bulgarian authorities seized the dark web sites used by the group. In October 2022, a Canadian affiliate, Sebastien Vachon-Desjardins, was sentenced to 20 years in prison.
Raccoon Stealer Developer Sentenced to 5 Years in Prison
In related law enforcement news, the DoJ also announced the sentencing of Mark Sokolovsky, a Ukrainian national accused of being the primary developer of the Raccoon Stealer malware, to 60 months in federal prison for one count of conspiracy to commit computer intrusion.
The 28-year-old conspired to offer the Raccoon infostealer as a malware-as-a-service (MaaS) to other criminal actors for $200 a month, who then deployed the malware on victims’ systems using various ruses such as email phishing in order to steal sensitive data. The harvested information was used to commit financial crimes or sold to others on underground forums.
Sokolovsky, who was extradited from the Netherlands in February 2024, pleaded guilty to the crime in early October and agreed to forfeit $23,975 and pay at least $910,844.61 in restitution.
“Mark Sokolovsky was a key player in an international criminal conspiracy that victimized countless individuals by administering malware which made it cheaper and easier for even amateurs to commit complex cybercrimes,” said U.S. Attorney Jaime Esparza for the Western District of Texas.
The U.S. Federal Bureau of Investigation (FBI) has set up a website where users can check whether their email address shows up in the data stolen by the Raccoon stealer malware. The MaaS operation was taken offline in March 2022 concurrent with Sokolovsky’s arrest by Dutch authorities.
NYC Man Gets Nearly 6 Years in Prison for Credit Card Trafficking and Money Laundering
The latest actions also follow the sentencing of a 32-year-old New York City man, Vitalii Antonenko, to time served plus days for his involvement in a criminal scheme that infiltrated systems with SQL injection attacks in order to steal credit card and personal information and offer the data for sale on online criminal marketplaces.
“Once a co-conspirator sold the data, Antonenko and others used Bitcoin as well as traditional bank and cash transactions to launder the proceeds in order to disguise their nature, location, source, ownership, and control,” the DoJ noted in May 2020. “The conspiracy’s victims included a hospitality business and non-profit scientific research institution, both located in eastern Massachusetts.”
Antonenko was arrested in March 2019 on his return to the U.S. from Ukraine carrying “computers and other digital media that held hundreds of thousands of stolen payment card numbers.”
In September 2024, he pleaded guilty to one count of conspiracy to gain unauthorized access to computer networks and to traffic in unauthorized access devices, and one count of money laundering conspiracy.
Found this article interesting? Follow us on
Twitter and
LinkedIn to read more exclusive content we post.