In January 2022, KrebsOnSecurity identified a Russian man named Mikhail Matveev as “Wazawaka,” a cybercriminal who was deeply involved in the formation and operation of multiple ransomware groups. The U.S. government indicted Matveev as a top ransomware purveyor a year later, offering $10 million for information leading to his arrest. Last week, the Russian government reportedly arrested Matveev and charged him with creating malware used to extort companies.

An FBI wanted poster for Matveev.
Matveev, a.k.a. “Wazawaka” and “Boriselcin” worked with at least three different ransomware gangs that extorted hundreds of millions of dollars from companies, schools, hospitals and government agencies, U.S. prosecutors allege.
Russia’s interior ministry last week issued a statement saying a 32-year-old hacker had been charged with violating domestic laws against the creation and use of malicious software. The announcement didn’t name the accused, but the Russian state news agency RIA Novosti cited anonymous sources saying the man detained is Matveev.
Matveev did not respond to requests for comment. Daryna Antoniuk at TheRecord reports that a security researcher said on Sunday they had contacted Wazawaka, who confirmed being charged and said he’d paid two fines, had his cryptocurrency confiscated, and is currently out on bail pending trial.
Matveev’s hacker identities were remarkably open and talkative on numerous cybercrime forums. Shortly after being identified as Wazawaka by KrebsOnSecurity in 2022, Matveev published multiple selfie videos on Twitter/X where he acknowledged using the Wazawaka moniker and mentioned several security researchers by name (including this author). More recently, Matveev’s X profile (@ransomboris) posted a picture of a t-shirt that features the U.S. government’s “Wanted” poster for him.
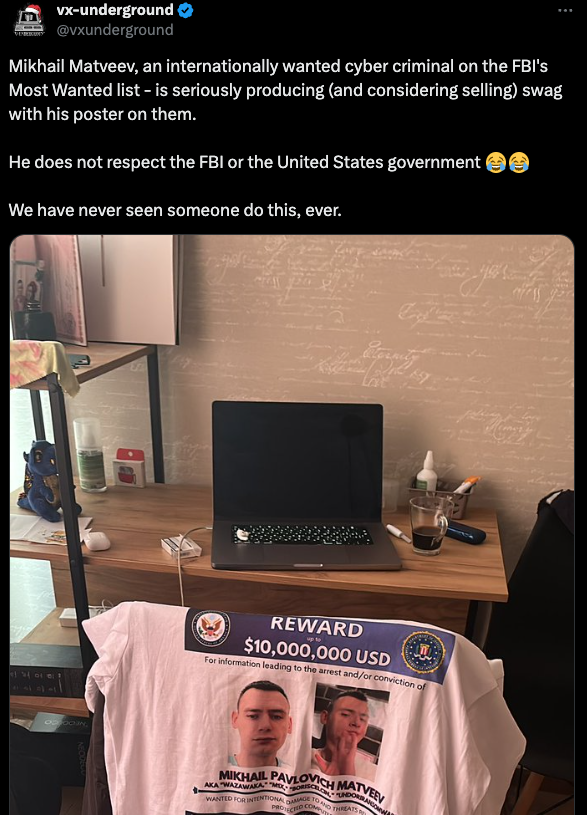
An image tweeted by Matveev showing the Justice Department’s wanted poster for him on a t-shirt. image: x.com/vxunderground
The golden rule of cybercrime in Russia has always been that as long as you never hack, extort or steal from Russian citizens or companies, you have little to fear of arrest. Wazawaka claimed he zealously adhered to this rule as a personal and professional mantra.
“Don’t shit where you live, travel local, and don’t go abroad,” Wazawaka wrote in January 2021 on the Russian-language cybercrime forum Exploit. “Mother Russia will help you. Love your country, and you will always get away with everything.”
Still, Wazawaka may not have always stuck to that rule. At several points throughout his career, Wazawaka claimed he made good money stealing accounts from drug dealers on darknet narcotics bazaars.
Cyber intelligence firm Intel 471 said Matveev’s arrest raises more questions than answers, and that Russia’s motivation here likely goes beyond what’s happening on the surface.
“It’s possible this is a shakedown by Kaliningrad authorities of a local internet thug who has tens of millions of dollars in cryptocurrency,” Intel 471 wrote in an analysis published Dec. 2. “The country’s ingrained, institutional corruption dictates that if dues aren’t paid, trouble will come knocking. But it’s usually a problem money can fix.
Intel 471 says while Russia’s court system is opaque, Matveev will likely be open about the proceedings, particularly if he pays a toll and is granted passage to continue his destructive actions.
“Unfortunately, none of this would mark meaningful progress against ransomware,” they concluded.
Although Russia traditionally hasn’t put a lot of effort into going after cybercriminals within its borders, it has brought a series of charges against alleged ransomware actors this year. In January, four men tied to the REvil ransomware group were sentenced to lengthy prison terms. The men were among 14 suspected REvil members rounded up by Russia in the weeks before Russia invaded Ukraine in 2022.
Earlier this year, Russian authorities arrested at least two men for allegedly operating the short-lived Sugarlocker ransomware program in 2021. Aleksandr Ermakov and Mikhail Shefel (now legally Mikhail Lenin) ran a security consulting business called Shtazi-IT. Shortly before his arrest, Ermakov became the first ever cybercriminal sanctioned by Australia, which alleged he stole and leaked data on nearly 10 million customers of the Australian health giant Medibank.
In December 2023, KrebsOnSecurity identified Lenin as “Rescator,” the nickname used by the cybercriminal responsible for selling more than 100 million payment cards stolen from customers of Target and Home Depot in 2013 and 2014. Last month, Shefel admitted in an interview with KrebsOnSecurity that he was Rescator, and claimed his arrest in the Sugarlocker case was payback for reporting the son of his former boss to the police.
Ermakov was sentenced to two years probation. But on the same day my interview with Lenin was published here, a Moscow court declared him insane, and ordered him to undergo compulsory medical treatment, The Record’s Antoniuk notes.
Source link



 Here’s how it happens.
Here’s how it happens.


 There is sense of proper nutritious food in Indian culture, everything was in control and in healthy proportion until the western food had come in directly as French fries type or indirectly as seed oils or sweeteners..
When you’re stressed and tired, healthy eating takes a back seat. It’s easier to grab junk food loaded with seed oils, preservatives, and artificial sweeteners like sucralose and maltodextrin. While these foods are convenient, they are also dangerous.
The high sugar content causes spikes and crashes in your blood sugar, leading to mood swings and irritability. Even worse, these chemicals promote insulin resistance and increase inflammation, which directly disrupts your
There is sense of proper nutritious food in Indian culture, everything was in control and in healthy proportion until the western food had come in directly as French fries type or indirectly as seed oils or sweeteners..
When you’re stressed and tired, healthy eating takes a back seat. It’s easier to grab junk food loaded with seed oils, preservatives, and artificial sweeteners like sucralose and maltodextrin. While these foods are convenient, they are also dangerous.
The high sugar content causes spikes and crashes in your blood sugar, leading to mood swings and irritability. Even worse, these chemicals promote insulin resistance and increase inflammation, which directly disrupts your 







 This is especially dangerous because many of these vulnerabilities are rated critical or high and are often easily exploitable. This practice aligns with the MITRE ATT&CK technique T1562 (Impair Defenses), which I’ve observed being used by APT groups to maintain persistence.
This is especially dangerous because many of these vulnerabilities are rated critical or high and are often easily exploitable. This practice aligns with the MITRE ATT&CK technique T1562 (Impair Defenses), which I’ve observed being used by APT groups to maintain persistence.
 From my analysis, this type of tool aligns with several MITRE ATT&CK techniques:
– T1027 (Obfuscated Files or Information)
– T1036 (Masquerading)
– T1556 (Modify Authentication Process)
I’ve noticed that APT groups are particularly adept at exploiting these gaps in vulnerability management to establish initial access (TA0001 in the MITRE ATT&CK framework) and maintain persistence (TA0003).
The takeaway here is clear: From everything I’ve observed, companies need to take a hard look at how they’re actually handling vulnerabilities. Implementing new security controls is great, but if you’ve got unpatched software or drivers, those controls can be bypassed. It’s time to prioritize staffing for vulnerability management and take a more proactive approach to patching. Otherwise, we’re just leaving the door wide open for APT groups to move through the entire kill chain undetected.
In my professional opinion, addressing this staffing issue isn’t just about security – it’s about survival in an increasingly hostile digital landscape. The APT groups I’ve been tracking are getting more sophisticated by the day, and understaffed security teams are fighting failing to fix vulnerability in time and an uphill battle they’re currently not equipped to win.
From my analysis, this type of tool aligns with several MITRE ATT&CK techniques:
– T1027 (Obfuscated Files or Information)
– T1036 (Masquerading)
– T1556 (Modify Authentication Process)
I’ve noticed that APT groups are particularly adept at exploiting these gaps in vulnerability management to establish initial access (TA0001 in the MITRE ATT&CK framework) and maintain persistence (TA0003).
The takeaway here is clear: From everything I’ve observed, companies need to take a hard look at how they’re actually handling vulnerabilities. Implementing new security controls is great, but if you’ve got unpatched software or drivers, those controls can be bypassed. It’s time to prioritize staffing for vulnerability management and take a more proactive approach to patching. Otherwise, we’re just leaving the door wide open for APT groups to move through the entire kill chain undetected.
In my professional opinion, addressing this staffing issue isn’t just about security – it’s about survival in an increasingly hostile digital landscape. The APT groups I’ve been tracking are getting more sophisticated by the day, and understaffed security teams are fighting failing to fix vulnerability in time and an uphill battle they’re currently not equipped to win. 

 Yes Beautiful.. : Observe them, Look at so many people how they lived… its the difference of living, or enjoying the life differently makes ones death different and impactful.
If Puneeth Rajkumar as some engineer or Aparna as some corporate CEO or lets consider Buddha as a king, Basavanna as a simple brahmin without inventing new community, Krishna as some a regular person of Yadav community would we have remembered them?
What made their death remember? all of them died in unnatural way or time… and beautiful thing is how differently they were and how the gods creative force was working through them!
(may be as I meditate on Shiva I get these thoughts 😆)
Conjunction of Material life and Spirituality: In the book Astral Body by AE Powell says, The poetic idea of death as a universal leveller is a mere absurdity born of ignorance, for, as a matter of fact, in the vast majority of cases, the loss of the physical body makes no difference whatever in the character of intellect of the person, and there are therefore as mind different varieties of intelligence among the so-called dead as among the living.
This is the first and the most prominent fact to appreciate: that after death there is no strange new life, but a continuation, under certain changed conditions, of the present physical plane life.
Many live by just performing day to day a activities and taking life so seriously that as if they take all up.. Create issue, go heartbreak, file a case on property, jealousy, anger, politics, family disagreements …all these seem so small and feels to avoid all these as I am looking at things happening day to day!
Because of the binding and slave mentality no one is daring or cpable to escape it, sad reality is there are so much entanglement in mind to escape all these…! Sometimes i even think.. what if i go out alone for some forest and just LIVE! or may be Go out explore the LIFE at Earth using this physical body!..
This article may sound crazy for some, insightful or anything.. which is mare reality till you live! 😆
Just while writing I remember this: I got insulted and humiliated by a lecturer in his chamber.. which only me and he knew.. and I was running it in my head for a year or so and was unable to look at him … after I moved to the UK.. all of sudden he was no more due to cancer… which again show how these emotions or the reality we think is so small!
So yea.. Just LIVE, Do you KARMA as Krishna said!
Yes Beautiful.. : Observe them, Look at so many people how they lived… its the difference of living, or enjoying the life differently makes ones death different and impactful.
If Puneeth Rajkumar as some engineer or Aparna as some corporate CEO or lets consider Buddha as a king, Basavanna as a simple brahmin without inventing new community, Krishna as some a regular person of Yadav community would we have remembered them?
What made their death remember? all of them died in unnatural way or time… and beautiful thing is how differently they were and how the gods creative force was working through them!
(may be as I meditate on Shiva I get these thoughts 😆)
Conjunction of Material life and Spirituality: In the book Astral Body by AE Powell says, The poetic idea of death as a universal leveller is a mere absurdity born of ignorance, for, as a matter of fact, in the vast majority of cases, the loss of the physical body makes no difference whatever in the character of intellect of the person, and there are therefore as mind different varieties of intelligence among the so-called dead as among the living.
This is the first and the most prominent fact to appreciate: that after death there is no strange new life, but a continuation, under certain changed conditions, of the present physical plane life.
Many live by just performing day to day a activities and taking life so seriously that as if they take all up.. Create issue, go heartbreak, file a case on property, jealousy, anger, politics, family disagreements …all these seem so small and feels to avoid all these as I am looking at things happening day to day!
Because of the binding and slave mentality no one is daring or cpable to escape it, sad reality is there are so much entanglement in mind to escape all these…! Sometimes i even think.. what if i go out alone for some forest and just LIVE! or may be Go out explore the LIFE at Earth using this physical body!..
This article may sound crazy for some, insightful or anything.. which is mare reality till you live! 😆
Just while writing I remember this: I got insulted and humiliated by a lecturer in his chamber.. which only me and he knew.. and I was running it in my head for a year or so and was unable to look at him … after I moved to the UK.. all of sudden he was no more due to cancer… which again show how these emotions or the reality we think is so small!
So yea.. Just LIVE, Do you KARMA as Krishna said!